Our Editors-in-Chief’s Top Picks
The Editors-in-Chief of our CASS publications have selected some noteworthy papers from the recent issues of our journals:
IEEE Transactions on Circuits and Systems I: Regular Papers
Paper 1:
D. Kim, H. Jeong, S. Kim, H. Yoon and K. J. Lee, "A Multibit ReRAM Computing-in-Memory Processor With Adaptive Decision Level Nonlinear ADC for Ultra-Low-Energy Keyword Spotting in Mobile Devices," IEEE Transactions on Circuits and Systems I: Regular Papers, vol. 73, no. 2, pp. 862-874, Feb. 2026, doi: 10.1109/TCSI.2025.3603076.
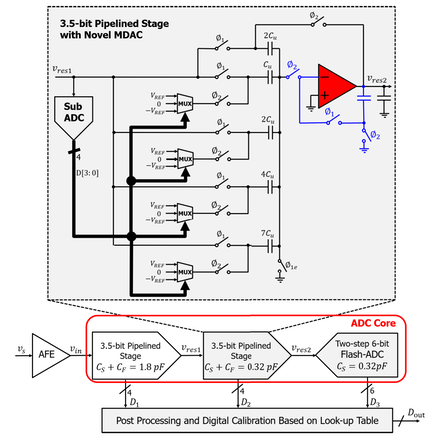
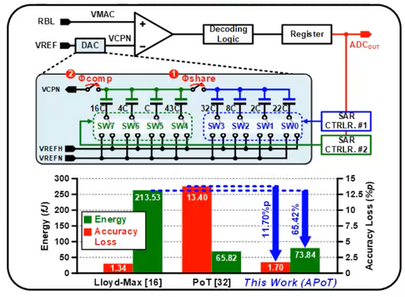
Summary: This paper introduces an ultra-low-energy keyword spotting (KWS) processor leveraging charge-mode multi-level ReRAM bitcells and adaptive ADC quantization. The proposed architecture reduces MAC energy by 61.39% while improving linearity by 1.65×. A 5-bit additive powers-of-two ADC cuts conversion energy by 65.42%, reduces accuracy loss by 11.70 percentage points, and boosts throughput by 1.33×. With pipelined layer fusion clusters minimizing memory footprint and increasing system throughput by 1.35×, the 45 nm CMOS implementation achieves 0.74 μJ per decision — a 55.15% reduction compared to prior KWS processors.
Paper 2:
S. Qiu, A. W. Hassan, M. Kinyua, E. G. Soenen and J. Silva-Martinez, "A 700 MS/s 12-bit Pipeline-ADC With a Sub-Range 6-bit Back-End Achieving 79 dB Signal-to-Distortion Ratio and FoM of 170.1 dB Near Nyquist Frequency," IEEE Transactions on Circuits and Systems I: Regular Papers, vol. 73, no. 3, pp. 1707-1720, March 2026, doi: 10.1109/TCSI.2025.3605848.
Summary: High-speed, high-resolution analog-to-digital converters (ADCs) are critical for broadband communication and sensing systems, yet achieving high efficiency at GS/s rates remains challenging. This work presents a 12-bit, 700-MS/s pipeline ADC that minimizes power through joint optimization of sampling capacitance, residue amplification, and comparator design. A class-AB residue amplifier with enhanced effective transconductance improves gain and bandwidth without additional power. A key innovation is a residue memory-enabled MDAC that intrinsically holds the residue voltage across an additional half clock cycle, effectively reusing the same analog state to support a time-multiplexed, two-step 6-bit flash backend. This implicit sample-and-hold reuse eliminates redundant circuitry and significantly reduces backend power. With digital calibration correcting residual errors, the prototype achieves high linearity and energy efficiency.
IEEE Transactions on Circuits and Systems II: Express Briefs
Paper 1:
D. Li, D. Li, Y. Yan, Y. Zhu, and Z. Zhu, “A Reconfigurable Voltage–Time Hybrid ADC With Quantization Threshold Shifting and Common-Mode Tracking,” IEEE Transactions on Circuits and Systems II: Express Briefs, vol. 73, no. 2, pp. 123-127, Feb. 2026. doi: 10.1109/TCSII.2025.3644154
Summary: Modern wireless systems such as smartphones and IoT devices must support multiple communication standards. This creates a growing demand for data converters that can adapt to different speed and resolution requirements. This brief presents a hybrid analog-to-digital converter (ADC) that combines voltage and time domains to realize flexible reconfiguration. The ADC also incorporates a quantization threshold shifting technique and a common-mode tracking circuit, enabling adjustable operation under multi-mode conditions and stable performance across a wide common-mode range. Fabricated in 65-nm CMOS, the 4-channel ADC can be configured into 4 modes, covering a resolution of 8-10 bits and a sampling rate of 1-4 GS/s.
Paper 2:
2. Y. Li, X. Yu, and R. Ni, “An 11.5-GHz 203.7-dBc/Hz FoMA Multi-Tap Inductor-Based Single-Core Fixed-Supply Reconfigurable VCO Achieving 8.2-dB PN Scaling,” IEEE Transactions on Circuits and Systems II: Express Briefs, vol. 73, no. 2, pp. 133 - 137, Jan. 2026. doi: 10.1109/TCSII.2025.3645575
Summary: Reconfigurable VCOs with scalable phase-noise (PN) and power consumption are critical for multi-protocol communication systems. This work presents a multi-tap inductor based PN-scaling (MIPS) technique that achieves PN and power-consumption scalability at a fixed supply voltage within a single-core area. By switching the drain connection to different taps of the tank inductor, the drain tank impedance is reconfigured, achieving scalable ISFeff, PN and power consumption. Fabricated in a 28-nm CMOS process with a core area of 0.053 mm2, the 11.5 GHz prototype MIPS VCO demonstrates an 8.2 dB PN and 3.4x power-consumption scalability across three operation modes.
Paper 3:
X. Chen, H. Zhu, Z. Liang, J. Zhang, D. Zeng, and S. Chen, “A 18.3–38.3-GHz Power Amplifier With Adaptive Dual-Voltage-Path Crossing Cold-FET Pair Achieving 22.7-dBm Psat and 31.9% PAE,” IEEE Transactions on Circuits and Systems II: Express Briefs, vol. 73, no. 3, pp. 248 - 252 248 - 252, Mar. 2026. doi: 10.1109/TCSII.2026.3656380
Summary: To address the challenges of wideband compatibility and linearity in 5G millimeter-wave (mm-wave) communications, this brief presents a wideband linear CMOS PA for 5G mm-wave applications. To improve linearity, an analog predistortion linearizer based on an adaptive dual-voltage-path crossing cold-FET pair (ADCCP) is proposed. By mutually cross-connecting the drain and gate of differential cold-FETs, the equivalent impedance is significantly enhanced. An adaptive bias circuit further controls the gate-source voltage of ADCCP, transitioning the transistor from saturation to turn-off region to boost linearity. Additionally, gain shaping technique is employed in transformer design to ensure wideband performance. The PA achieves a 3-dB bandwidth of 18.3–38.3 GHz, peak gain of 20.8 dB, saturated output power Psat of 22.7 dBm, and peak PAE of 31.9%.
IEEE Transactions on Circuits and Systems for Video Technologies
Paper 1:
Yimin Fu, Runqing Yang, Zhunga Liu, Michael K. Ng. "Adaptive Mixture-of-Experts Distillation for Cross-Satellite Generalizable Incremental Remote Sensing Scene Classification," IEEE Trans. on Circuits and Systems for Video Technology, vol.36, no.1, pp.233-247, Jan. 2026. doi: 10.1109/TCSVT.2025.359827.

This paper proposes adaptive mixture-of-experts distillation (AMoED) for cross-satellite generalizable incremental remote sensing scene classification (CS-GIRSSC). Specifically, AMoED adopts a high-level semantic learning pipeline, in which new knowledge is acquired through the coordinated guidance of multiple domain-specific experts, rather than directly from raw data. This pipeline prevents the model from being exposed to large volumes of newly emerging data, thereby alleviating the erasure of previous knowledge when adapting to new data distributions. Besides, the adaptive mixture of domain-specific experts facilitates the formation of universal class concepts, which exhibit strong generalizability across different domains. During the learning process, an equi-partite subset is constructed for knowledge acquisition and consolidation, accompanied by a shallow style-mixing operation to mitigate the interference of domain discrepancies. Extensive experiments have been conducted on four remote sensing scene classification datasets, and the method proposed in this paper consistently shows state-of-the-art performance across various scenarios and settings. The code has been also made available by the authors at https://github.com/fuyimin96/AMoED
Paper 2:
Xiao Wang, Chao Wang, Shiao Wang, Xixi Wang, Zhicheng Zhao, Lin Zhu. "MambaEVT: Event Stream-Based Visual Object Tracking Using State Space Model," IEEE Trans. on Circuits and Systems for Video Technology, vol.36, no.1, pp.278-291, Jan. 2026. doi: 10.1109/TCSVT.2025.3588533.
This paper proposes a Mamba-based visual tracking framework that adopts the state space model with linear complexity as a backbone network. The search regions and target template are fed into the vision Mamba network for simultaneous feature extraction and interaction. The output tokens of search regions will be fed into the tracking head for target localization. More importantly, a dynamic template update strategy is introduced into the tracking framework using the Memory Mamba network. By considering the diversity of samples in the target template library and making appropriate adjustments to the template memory module, an effective dynamic template can be integrated. The effective combination of dynamic and static templates allows the proposed Mamba-based tracking algorithm to achieve a good balance between accuracy and computational cost on multiple large-scale datasets, including EventVOT, VisEvent, and FE240hz. The source code and checkpoint of this work have been released on https://github.com/Event-AHU/MambaEVT

Overview of the proposed pure Mamba-based visual object tracking using an event camera, termed MambaEVT. The vision Mamba based backbone network performs feature extraction, interaction and fusion, simultaneously. It ensures the tracker achieves good performance and lowers computational cost. The learnable Memory Mamba for dynamic template generation makes the tracker more robust to significant appearance variation.
Paper 3:
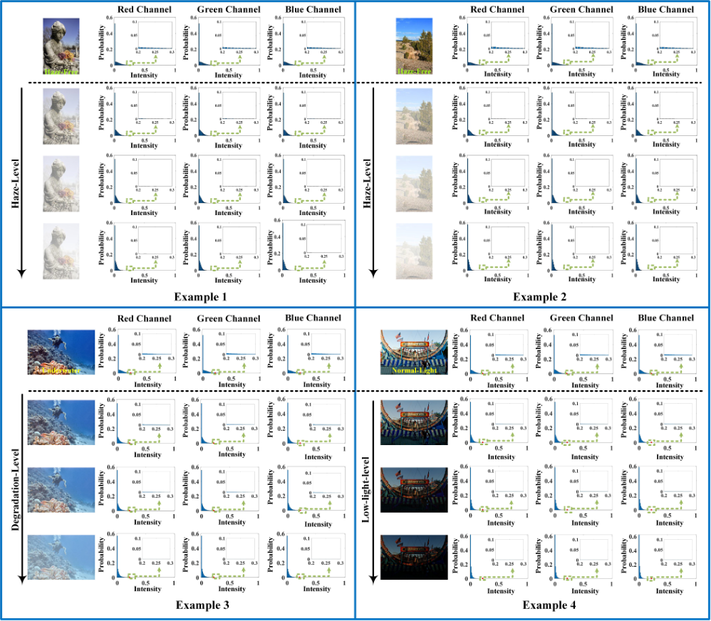
Nian Wang, Zhigao Cui, Yanzhao Su, Yunwei Lan, Yuanliang Xue, Cong Zhang. "Weakly Supervised Image Dehazing via Physics-Based Decomposition," in IEEE Trans. on Circuits and Systems for Video Technology, vol.36, no.1, pp.637-652, Jan. 2026, doi: 10.1109/TCSVT.2025.3596024.
This paper proposes a weakly supervised image dehazing (WSID) model via physics-based decomposition (PBD). The proposed approach estimates atmospheric light, scattering coefficient and scene depth of real haze input to effectively capture the illumination information and haze distribution to recover a preliminary dehazed image by minimizing reconstruction loss. With this constraint, a subtly discrete wavelet discriminator (DWD) is designed to effectively improve the generalization to real scene from both spatial and frequency aspect under the supervision of unpaired real clear image. The PBD is a purely data-driven model freeing from any manual setting or partially correct prior, thus simultaneously ensuring the realness and visibility of dehazed images. Experiments on seven benchmarks have been reported in the paper showing the strong generalization ability of the proposed PBD, which achieves SOTA dehazing performance with realistic details. The code has been made available by the authors at the following link at https://github.com/NianWang-HJJGCDX/PBD
Workflow of the PBD proposed in this paper. First, four generators are used to yield the dehazed image Jout, scattering coefficient β, scene depth D, global atmospheric light A. The β and D capture the haze distribution of input real haze image Ireal and obtain a refined transmission map T. Reconstruction loss is used to constrain the structure information of these parameters. Then DWD improves the generalization ability of Jout and makes it fit in various real haze scenes via the adversarial training from both spatial and frequency aspect.
IEEE Transactions on Very Large Scale Integration (VLSI) Systems
Paper 1:
Das, S., Riedel, S., Naeim, M., Brunion, M., Bertuletti, M., Benini, L., Ryckaert, J., Myers, J., Biswas, D. and Milojevic, D., 2024. "Bandwidth-Latency-Thermal Co-Optimization of Interconnect-Dominated Many-Core 3D-IC," IEEE Transactions on Very Large Scale Integration (VLSI) Systems. vol. 33, no. 2, pp. 346-357, Feb. 2025, doi: 10.1109/TVLSI.2024.3467148 https://ieeexplore.ieee.org/document/10720515
Summary: The article addresses the challenges faced by contemporary system-on-chips (SoCs) due to the increasing demands for memory bandwidth, capacity, and thermal stability, particularly in the context of advancing artificial intelligence (AI). It proposes architectural modifications for a many-core SoC designed to enhance on-chip cache memory bandwidth and optimize access latency. The SoC is fabricated using A10 nanosheet technology in a 3-D configuration, with thermal analyses conducted. Workload simulations demonstrate significant performance improvements, achieving up to 12-fold acceleration for a 64-core version and 2.5-fold for a 16-core version, accompanied by a 40% increase in die area and a 60% rise in power dissipation when using a 2-D design. In comparison, the 3-D design not only minimizes the physical footprint but also saves 20% in power consumption due to a 40% reduction in wirelength. The study emphasizes the importance of restructuring pipelines to optimize the benefits of 3-D technology for enhanced memory access and lower latency. Additionally, it explores thermal impacts of different 3-D partitioning approaches in high-performance computing (HPC) and mobile applications, finding that 3-D designs in mobile contexts only slightly increase maximum temperature (by about 2-3 °C) compared to 2-D, while HPC scenarios require careful partitioning strategies to effectively manage thermal constraints.
Paper 2:
G. Murali, M. Gyu Park and S. Kyu Lim, "3DNN-Xplorer: A Machine Learning Framework for Design Space Exploration of Heterogeneous 3-D DNN Accelerators," IEEE Transactions on Very Large Scale Integration (VLSI) Systems, vol. 33, no. 2, pp. 358-370, Feb. 2025, doi: 10.1109/TVLSI.2024.3471496. https://ieeexplore.ieee.org/document/10715720
Summary: This paper introduces 3DNN-Xplorer, a novel machine learning (ML)-based framework for predicting the performance of heterogeneous 3-D deep neural network (DNN) accelerators. This framework enables design space exploration (DSE) of these accelerators with a two-tier compute-on-memory (CoM) configuration, considering 3-D physical design factors. The framework explores four distinct heterogeneous 3-D integration styles combining 28-nm and 16-nm technology nodes for both compute and memory tiers. Through extrapolation techniques and ML models trained on various accelerator configurations, the performance of larger systems is estimated, achieving a maximum absolute error of 13.9%. The framework considers area imbalance arising from different technology nodes by assuming equal numbers of PEs or on-chip memory capacity across integration styles. The analysis reveals that the heterogeneous 3-D style with 28-nm compute and 16-nm memory demonstrates energy-efficient performance, offering up to 50% energy savings and an 8.8% reduction in runtime compared to other 3-D integration styles. Conversely, the heterogeneous 3-D style with 16-nm compute and 28-nm memory proves area-efficient, exhibiting up to 8.3% runtime reduction compared to other 3-D styles.
Paper 3:
A. Almeida da Silva, L. Nogueira, A. Coelho, J. A. N. Silveira and C. Marcon, "Securet3d: An Adaptive, Secure, and Fault-Tolerant Aware Routing Algorithm for Vertically–Partially Connected 3D-NoC," IEEE Transactions on Very Large Scale Integration (VLSI) Systems, vol. 33, no. 1, pp. 275-287, Jan. 2025, doi: 10.1109/TVLSI.2024.3500575 https://ieeexplore.ieee.org/document/10766899
Summary: This article presents Securet3d, a novel routing algorithm designed for multiprocessor systems-on-chip (MPSoCs) that utilize 3-D networks-on-chip (3D-NoCs), aimed at enhancing secure and fault-tolerant operations. As MPSoCs play a crucial role in achieving effective parallel computing by sharing resources across complex applications, implementing adaptive mechanisms to safeguard sensitive data is essential. Securet3d builds upon the existing Reflect3d algorithm, introducing a comprehensive mapping scheme for secure data pathways and improving the system’s fault tolerance. The algorithm's effectiveness is validated through comparisons with three other fault-tolerant routing algorithms in vertically-partially connected 3D-NoCs. All algorithms were developed in SystemVerilog and evaluated via simulations using ModelSim, and hardware synthesis was performed with Cadence’s Genus tool. The experimental results indicate that Securet3d not only reduces latency but also enhances cost-effectiveness compared to other methods. Implemented with a 28-nm technology library, Securet3d exhibits minimal area and energy overhead, demonstrating its scalability and efficiency. Moreover, during denial-of-service (DoS) attacks, Securet3d maintains relatively stable average packet latencies of 70, 90, and 29 clock cycles for uniform random, bit-complement, and shuffle traffic, respectively, which are significantly lower than the latencies observed in other algorithms lacking security mechanisms (5763, 4632, and 3712 clock cycles on average). These findings underscore Securet3d's superior security, scalability, and adaptability for complex communication systems.
IEEE Journal on Emerging and Selected Topics in Circuits and Systems
Paper 1:
Z. Xin, J. Zhang, M. Zhu, Q. Zhong, M. Lei, and B. Hua, "520-Gbit/s Optical-Terahertz Integration System for Cable-Free Data Centers Utilizing Adaptive Bayes-Adam MIMO Nonlinear Equalizer," IEEE Journal on Emerging and Selected Topics in Circuits and Systems, vol. 16, no. 1, pp. 15-26, March 2026, doi: 10.1109/JETCAS.2025.3640639. https://ieeexplore.ieee.org/document/11278661
Summary: To meet the growing demands of next-generation data centers for ultra-high capacity, low latency, and flexible deployment, optical-wireless integrated systems combine the high bandwidth of fiber with the agility of wireless links, enabling scalable and high-speed interconnect solutions. Polarization division multiplexing (PDM) single-input single-output (SISO) links have a simplified architecture design and can double the system capacity through the polarization dimension, but they also introduce more crosstalk and impairments to signal recovery. In this paper, an adaptive Bayes-Adam (ABA) multiple-input multiple-output (MIMO) Volterra nonlinear equalizer (VNE) with high precision and fast convergence is proposed, which better compensates for crosstalk and impairments in dual-polarization (DP) SISO terahertz (THz) transmission systems, including I/Q imbalance, polarization crosstalk, and nonlinear distortion. We experimentally demonstrate a DP-SISO fiber-THz integrated system, which adopts an easily integrable zero-intermediate frequency (Zero-IF) receiver front-end scheme to reduce bandwidth requirements and efficiently receive high baud rate signals. By employing the novel equalization algorithm, we successfully achieve up to 520 Gbit/s single-lane single-carrier wireless air interface rate (WAIR/ch) at 220 GHz with a 20% soft-decision forward error correction (SD-FEC) threshold. This work provides an effective signal processing solution for enabling high-speed, scalable fiber- THz interconnects in future data center networks.

Paper 2:
D. Najafi, H. e. Barkham, Z. Ghanaatian, M. Morsali, H. Chen, T. Das, A. Roohi, P. Mercati, M. Nikdast, M. Imani, and S. Angizi, "Opto-Aligner: Optical Near-Sensor Architecture for Accelerating DNA Pre-Alignment Filtering," IEEE Journal on Emerging and Selected Topics in Circuits and Systems, vol. 16, no. 1, pp. 124-136, March 2026, doi: 10.1109/JETCAS.2025.3619017. https://ieeexplore.ieee.org/document/11196950
Summary: Sequence alignment, a cornerstone application in bioinformatics, is critical for enabling personalized medicine and disease diagnostics. However, the rapid growth of genomic data has led to significant computational challenges, including limited throughput, high latency, and excessive data movement in current sequencing solutions. To address these issues, we propose Opto-Aligner, a high-performance and energy-efficient optical near-sensor accelerator framework tailored for multiple genetic tasks, mainly as DNA/RNA pre-alignment filtering in hyperdimensional space. Opto-Aligner harnesses Silicon Photonics’ promising efficiency and hyperdimensional computing (HDC) robustness to accelerate genome sequence alignment directly at the sensor level. We develop innovative microarchitectural and circuit-level solutions, including specialized hardware partitioning and mapping strategies, to overcome challenges inherent in photonic computing—our cross-layer design accounts for photonic device variability and noise, optimizing HDC algorithms for optical hardware constraints. Opto-Aligner significantly improves throughput and energy efficiency over leading electronic DNA aligners. Relative to the best published electronic aligner (BioHD-HAM), Opto-Aligner delivers a 5.7× higher single-die throughput (0.93 Mb s−1 vs. 0.163 Mb s−1) and a 3.0×10 5 -fold reduction in energy–delay product, all with sub-nanosecond comparator latency and seamless scaling to multi-bit precision. Opto-Aligner effectively bridges the gap between the computational demands of genome alignment and the limitations of optical hardware.
Paper 3:
R. Asquini, A. Buzzin, B. Alam, A. Ceschini, A. Rosato and M. Panella, "All-optical AND Logic Gate With High Extinction Ratio for Neural Network Hardware Implementation," IEEE Journal on Emerging and Selected Topics in Circuits and Systems, vol. 16, no. 1, pp. 106-114, March 2026, doi: 10.1109/JETCAS.2025.3623865. https://ieeexplore.ieee.org/document/11208673
Summary: The development of optical logic gates suitable for multi-stage processes is a central issue in emerging computational applications such as optical neural networks. In this work, we introduce and analyze a scheme for an all-optical AND logic gate, which allows achieving an almost ideal extinction ratio, a feature that simplifies cascaded architectures for complex operations such as multibit sums and multiplications. We analytically demonstrate how our scheme forces three logical states, namely ‘00’, ‘11’ and ‘10’, to be necessarily ideal in behavior. We also outline the conditions for ideal behavior of the remaining logical state ‘01’, which requires the use of semiconductor optical amplifiers (SOA) in their non-linear operations, by tuning the optical input and feeding current. Our numerical analysis on symmetrically balanced SOAs shows that there are multiple conditions enabling a very small output at logical ‘01’; also, our results suggest that those solutions are strongly influenced by the phase shifts induced in SOAs, which requires to avoid small α factors. The performance outlined in our transitions are promising for the implementation of universal gates to be deployed in future architectures for neural optical computation.
IEEE Open Journal of Circuits and Systems
Paper 1:
T. Kaiser, E. Gottschalk, K. Biethahn and F. Gerfers, "Pasithea-1: An Energy-Efficient Sequential Reconfigurable Array With CPU-Like Programmability," IEEE Open Journal of Circuits and Systems, vol. 6, pp. 1-13, 2025, doi: 10.1109/OJCAS.2024.3518110. https://ieeexplore.ieee.org/document/10802954
Summary: This work presents Pasithea-1, a coarse-grained reconfigurable array (CGRA) that combines energy efficiency with CPU-like programmability.
Paper 2:
B. Yang, T. Caldwell and A. Chan Carusone, "An Energy-Efficient Pipeline-SAR ADC Using Linearized Dynamic Amplifiers and Input Buffer in 22nm FDSOI," IEEE Open Journal of Circuits and Systems, vol. 6, pp. 50-62, 2025, doi: 10.1109/OJCAS.2024.3509746. https://ieeexplore.ieee.org/document/10774063
Summary: This work presents a dynamic amplifier that achieves −52 dB in total harmonic distortion through an analog technique by which the expanding and compressing nonlinearities in the input transistors cancel one another. A pipeline-SAR analog-to-digital converter incorporating the linearized dynamic amplifier in both the input buffer and the first residue amplifier stage was designed and fabricated using the GlobalFoundries 22nm fully depleted silicon-on-insulator process.
Paper 3:
S. Nowshin Chowdhury, M. Chen and S. Shah, "Analysis and Verilog-A Modeling of Floating-Gate Transistors," IEEE Open Journal of Circuits and Systems, vol. 6, pp. 63-73, 2025, doi: 10.1109/OJCAS.2024.3524363. https://ieeexplore.ieee.org/document/10818976
Summary: This work presents a Verilog-A model based on empirical measurements for a floating-gate transistor fabricated using a 65 nm CMOS process.
________________
IEEE CAS Magazine First Quarter Issue 2026
Now available: First Quarter Issue
IEEE Circuits and Systems (CAS) Magazine publishes original review articles and other articles that are of broad interest to the Circuits and Systems Society community. Interested authors are invited to send a three to four page White Paper first to the Editor-in-Chief, Prof. Keshab K. Parhi, by email here. If invited, they can submit a Full Paper at the Author Portal at the link below. CAS Magazine will continue to publish articles related to CAS Society Outreach. In addition, CAS Magazine also publishes articles related to education (such as tricks in solving problems and short lecture notes), conference highlights, chapter highlights, applications, and standards. Please feel free to submit articles that are of broad interest to the members of the CAS Society. For more information, please visit the IEEE Circuits and Systems Magazine on the CASS website.
________________
Call for Papers: IEEE Journal of Selected Topics in Signal Processing (JSTSP) Special Issue on "Autonomous and Evolutive Optimization in Networked AI"
The IEEE Journal of Selected Topics in Signal Processing (JSTSP) is inviting submissions to a special issue on "Autonomous and Evolutive Optimization in Networked AI”.
The issue focuses on autonomous optimization algorithms, evolutive learning, networked AI systems, and their applications in signal processing, communications, AI, and embedded systems.
Submission deadline: June 15, 2026. Please click here for details.
________________
Active "Call for Papers” Archive
______________________________
Latest Tables of Contents of CAS Sponsored Journals
The latest issues of our CAS sponored journals have been published and the tables of contents can be accessed through the following links:

- IEEE Transactions on Circuits and Systems I: Regular Papers
- IEEE Transactions on Circuits and Systems II: Express Briefs
- IEEE Transactions on Circuits and Systems for Video Technology
- IEEE Journal on Emerging and Selected Topics in Circuits and Systems
- IEEE Circuits and Systems Magazine
- IEEE Transactions on Biomedical Circuits and Systems
- IEEE Design and Test Magaz
